The Security Architecture of GitHub Agentic Workflow
- CI/CD pipelines are built on a simple assumption. The developers define the steps, the system runs them, and every execution is predictable.
- Agents break that assumption completely because they don’t follow a fixed script.
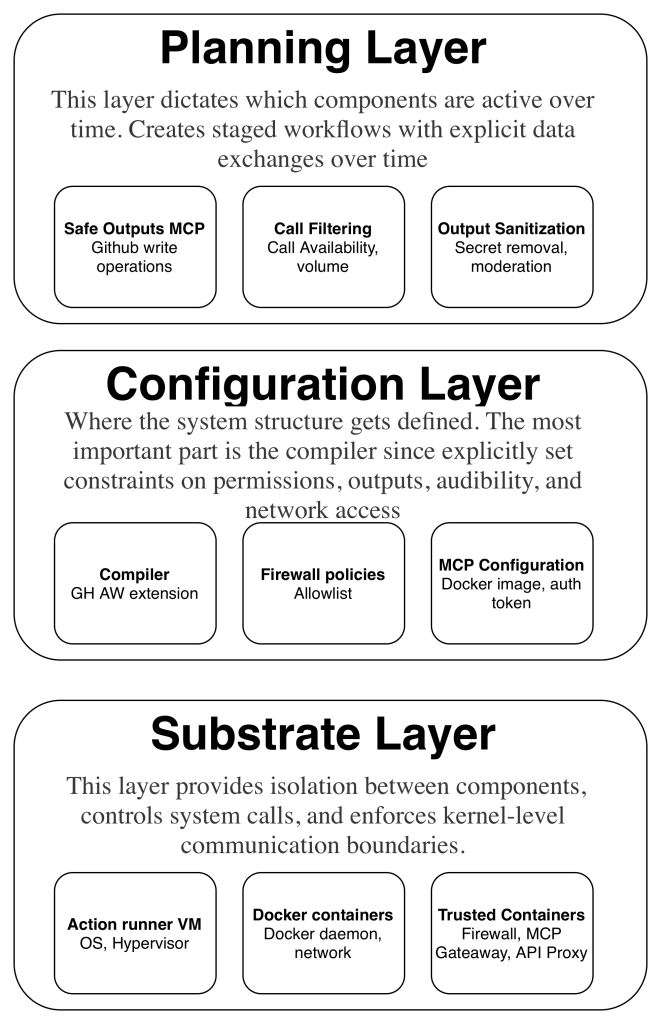
- GitHub Agentic Workflows use a layered security architecture with three distinct levels.
- Github is not the only one hiding secrets to agents. OpenAI’s Codex takes a different path to the same destination. In the Codex cloud, secrets are available only during the setup phase and are removed before the agent phase starts, and internet access is disabled by default during execution. GitHub uses proxies and gateways. OpenAI uses a two-phase model.
The absence of secrets doesn’t mean the absence of risk.
Github Safe outputs system
- The agent can read GitHub state through the GitHub MCP server, which operates in read-only mode. But it cannot write to GitHub directly.
- Once the agent finishes its work and exits, everything it staged goes through a deterministic analysis pipeline:
- Check each operation against an allowlist that the workflow author defined.
- Enforce quantity limits.
- Run content sanitization